SME Cybersecurity: Can NordLayer Browser cut phishing, shadow IT, and SaaS risk for UK SMEs?
April 23, 2026






Gibraltar: Thursday, 23 April 2026 – 07:00 CET
SME Cybersecurity: Can NordLayer Browser cut phishing, shadow IT, and SaaS risk for UK SMEs?
By: Iain Fraser – Cybersecurity Journalist
Published in Collaboration with:
Securus Technology Group
SMECyberInsights.co.uk – First for SME Cybersecurity
Google Indexed on: xxxxx at xxxx
#SMECyberInsights #SMECybersecurity #SMECyberInsights #SME #CyberSafe #CyberSecurity #Cybersecurity #NordLayer #SecureBrowser
SME Cybersecurity: Can NordLayer Browser cut phishing, shadow IT, and SaaS risk for UK SMEs?
The modern UK SME does not “use the internet”; it runs the business inside it. Email, finance approvals, CRM, HR portals and supplier invoices all happen in a browser tab, often on a mix of managed laptops and personal devices. Attackers have adapted faster than most policies. The UK Government’s Cyber Security Breaches Survey 2025 reports 43% of businesses experienced a cyber breach or attack in the last 12 months, with phishing the most common entry route.
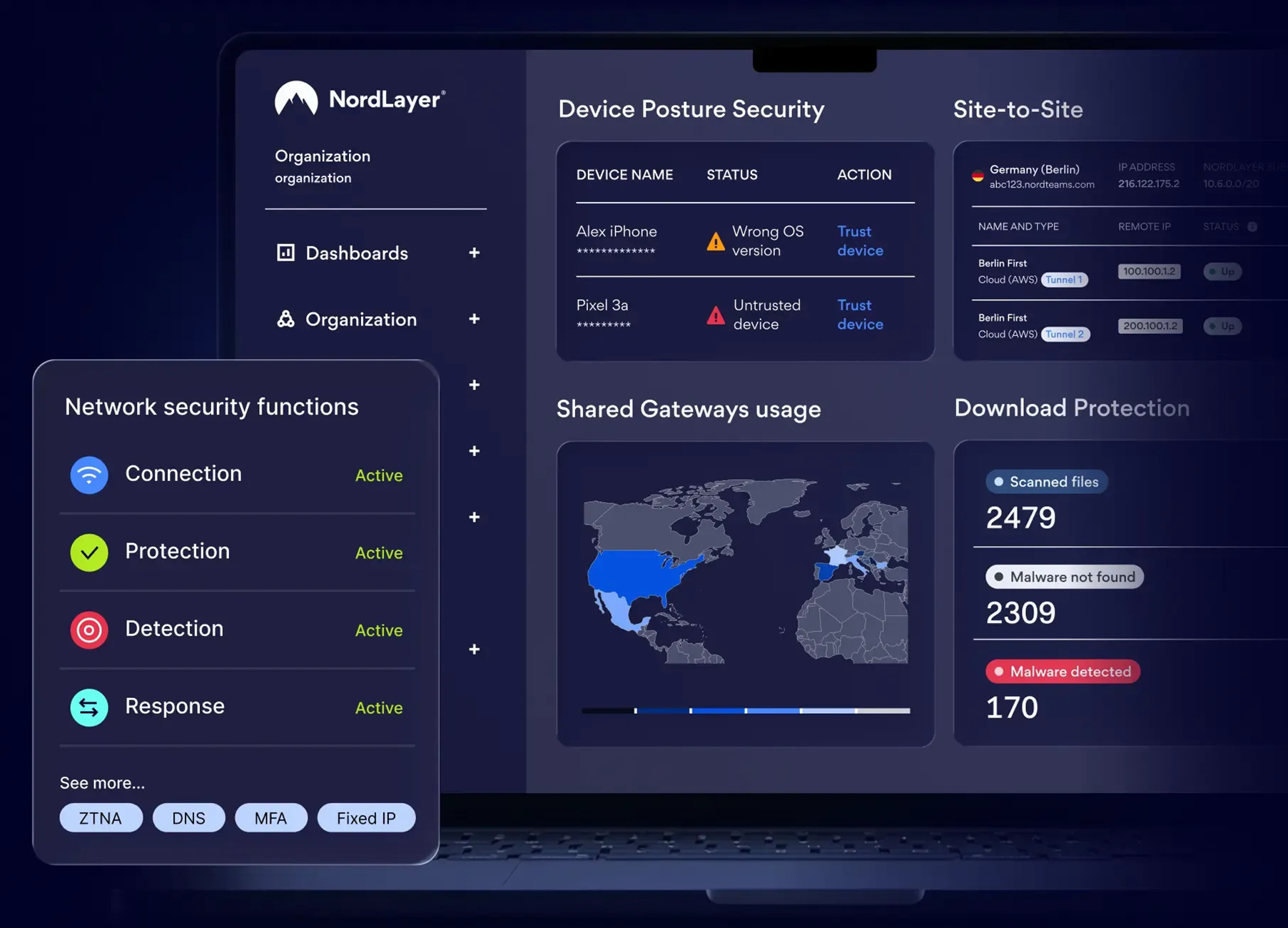
That context explains why NordLayer Browser is an interesting development for SME Cybersecurity. The pitch is straightforward: a business-focused browser that aims to make advanced security easier to deploy and manage for SMEs, without turning every improvement into a full endpoint project. (Source:)
What is a “Secure Business Browser”, in plain English?
A secure business browser is a centrally managed web browser designed for work use. It gives IT or your managed service provider a way to apply policies consistently, reduce risky behaviours, and improve visibility into browser-based work.
For a typical SME, the risk is not theoretical. One compromised mailbox can lead to business email compromise, supplier payment diversion, or customer data exposure. A browser is where credentials are entered, files are downloaded, and extensions quietly gain permissions.
NordLayer’s launch coverage describes the concept as a browser tailored for business security outcomes, particularly around streamlining controls for SMEs and MSP-led deployments.
How does browser risk show up in real UK SME incidents?
In practice, browser-led risk tends to cluster into three issues that repeatedly appear in SME incident response:
* Phishing protection for SMEs: Fake Microsoft 365 or Google login pages steal credentials, then criminals set mailbox forwarding rules and watch invoice traffic.
* Extension sprawl: Staff install unapproved PDF tools, meeting add-ons, and “AI helpers” that can read pages and access data.
* Shadow IT and supply chain cyber risk: Teams sign up to SaaS tools with personal emails, then client data ends up outside any contract, retention rule, or exit plan.
NCSC guidance on phishing focuses on recognising malicious messages and reporting quickly to reduce harm. Speed matters more than certainty, especially when finance teams are under pressure.
What Cyber Essentials controls should you prioritise alongside a secure browser?
A secure browser can help, but it should sit on top of solid basics. Cyber Essentials remains the most practical UK baseline for SMEs because it focuses on controls that reduce common attacks: secure configuration, security update management, access control, malware protection, and firewalls.
If you are choosing where to invest first, prioritise:
* MFA (multi-factor authentication) for email and key SaaS, because it blocks many account takeovers even when passwords leak.
* Removal of shared admin accounts, because shared access destroys accountability and makes containment slower.
* Patch discipline on endpoints, because browser exploits and drive-by downloads still rely on known vulnerabilities.
Actionable guidance: a 30-day rollout plan that fits SME reality
Treat NordLayer Browser as a targeted control for your highest-risk workflows, not a “big bang” change.
1. Pilot with two roles: Finance and Directors
These are the people criminals target for invoice fraud and urgent payment requests.
2. Create an approved SaaS list, then enforce it
Decide what is allowed for file sharing, e-signatures, password management and client communications. Block the rest, or route exceptions through a simple approval.
3. Allow-list extensions only
Remove everything not needed for work. If an extension requests broad permissions, treat it like software procurement, not a personal preference.
4. Pair browser policy with incident-ready reporting
Make it easy to report suspicious emails and links, and practice what happens next. NCSC provides clear guidance on phishing response.
5. Map outcomes to UK GDPR security measures
If you handle personal data, the ICO expects appropriate technical and organisational measures. Centralised control of browser access and behaviour can support that, alongside training and access reviews.
Run a 14-day pilot of NordLayer Browser with Finance and one client-facing team; measure phishing reports, unapproved SaaS usage, and extension count before and after, then decide whether to scale.
SECURUS Communications Ltd
Securus is a managed communications Operator, providing next-generation network infrastructure and value added services to Managed Hosting providers and the ‘cloud generation’ of enterprises. Securus priority is to offer communication services that represent excellent value for money and are backed by exceptional levels of support.
Contact Securus
Securus Communications Ltd
Station Road, Landmark house, Hook, England RG27 9HA, GB
T: Enquiries: 03451 283457 | Service Desk: 03451 283458
Securus on LinkedIn | Securus on “X” | https://securuscomms.com